Five steps every new Debian or Ubuntu server needs
If you are setting up a new server here are some basic but crucial steps that are needed to be prepare your Ubuntu 14.04 for running securely and smoothly.
0. Remove Ubuntu and install Debian :)
Step 0 was added by popular demand by few senior admins who suggested not to ever use Ubuntu as server :)
I can't argue with that, when I have the choice I usually install Debian or Centos, depending of the task or service which will be used.
1. Make sure server is updated
apt-get update && apt-get upgrade
2. Change ssh service to different port, add your public key and disable password logins.
vim /etc/ssh/sshd_config
change from Port 22 to some port you will remember :) Best to use some random port in range 10000-65535. We will call this number <ssh-port>.
Changing ssh port won't give you added security if you are attached by a targeted attack, but it will definitely lover the noise in your logs because most scripts just try ssh on port 22 an move along if they don't find service running on port 22.
Copy your public ssh key from ~/.ssh/id_rsa.pub to your servers /root/.ssh/authorized_keys file.
Edit /etc/ssh/sshd_config and change
#PasswordAuthentication yes
to
PasswordAuthentication no
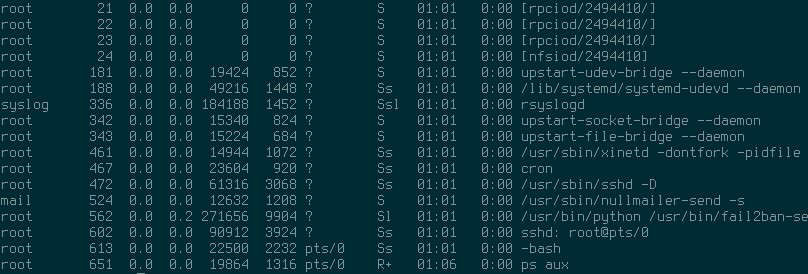
3. Install, configure and enable fail2ban
apt-get install fail2ban
vim /etc/fail2ban/jail.conf
Now change bantime and findtime to 86400, scroll down to [ssh] part and change port = 22 to <ssh-port>.
Now enable fail2ban so it start on boot:
update-rc.d fail2ban enable
And then check to see the status of how many IPs you have caught and blocked:
fail2ban-client status ssh
4. Install and configure nullmailer
Nullmailer is an awesome software, simple, elegant, secure, small and gets the job done. If you have a dedicated server for email, or want to use your service providers email server, or even Gmail to send out mails then nullmailer is what you want.
apt-get install nullmailer
Make sure you use secure ways of connecting to you smtp server, for example if you use Gmail then your /etc/nullmailer/remotes should look like this:
smtp.gmail.com smtp --port=587 --auth-login --user=you@gmail.com --pass=Yourpassword --starttls
5. Block all ports
Use these simple iptables settings to close all ports, except your <ssh-port>, of course.
iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A INPUT -p tcp --dport <ssh-port> -j ACCEPT
iptables -P INPUT DROP
Now save your rules:
iptables-save > /etc/iptables
And edit /etc/rc.local so your iptables firewall rules are loaded on boot, add this line before exit 0:
iptables-restore < /etc/iptables
Bonus: 6. Change locale
If you use German VPS providers like me then you won't be surprised that defualt locale is set to LANG=de_DE.UTF-8. Interestingly enough Ubuntu documentation for changing default locale is lacking crucial information. First install locale you need:
apt-get install language-pack-en
To check installed locales on your system list them with:
locale -a
On Debian build and configure locales with this command:
dpkg-reconfigure locales
For Ubuntu change default locale by editing these two files:
vim /etc/default/locale
I changed from LANG=de_DE.UTF-8 to LANG="en_US" and also
vim /etc/profile
from
export LANG="de_DE.utf8"
export LANGUAGE="de_DE.utf8"
export LC_ALL="de_DE.utf8"
to
export LANG="en_US.utf8"
export LANGUAGE="en_US.utf8"
export LC_ALL="en_US.utf8"
Links: